Shared Assessments has released its updated 2019 Third Party Risk Management Toolkit which serves organizations for vendor risk management, regardless of size and industry. The Toolkit elements help both outsourcers and providers to meet regulatory, consumer and business scrutiny within the constantly evolving landscape of cyber and other security threats and vulnerabilities.
Shared Assessment keeps a close eye on emerging regulations, guidelines and standards for a wide range of industries, such as: NIST 800-53r4, NIST CSF 1.1, FFIEC CAT Tool and PCI 3.2.1. That knowledge is used to update the new Toolkit, which embodies multiple Tools for a comprehensive “trust, but verify” approach for conducting third party risk management assessments, using a substantiation-based, standardized, efficient methodology.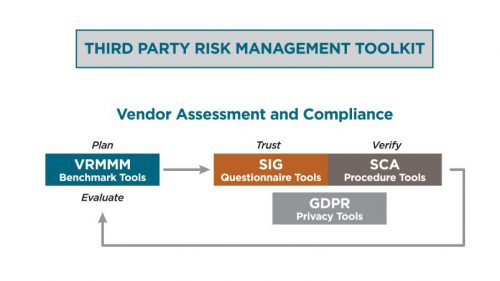
The 2019 Third Party Risk Management Toolkit includes:
2019 Standardized Information Gathering (SIG) Questionnaire Tools
2019 Standardized Control Assessment (SCA) Procedure Tools
2019 Vendor Risk Management Maturity Model (VRMMM) Benchmark Tools
2019 General Data Protection Regulation (GDPR) Privacy Tools
Changes to the Toolkit were determined by the collective intelligence of our membership, bringing a diversity of views from;
- Outsourcers, service providers, licensees, assessment firms and regulators.
- Organizations from start-ups to large, global corporations.
- Industries such as Financial, Insurance, Consumer Packaged Goods, Services, IT and Healthcare.
- Subject experts in cybersecurity, privacy, supply chain risk, compliance, regulation, enterprise risk management and third party risk.
The updates for 2019 are a response not only to the changing regulatory and risk landscape, but to our hundreds of members and tool purchasers looking to perform vendor risk assessments that provide assurance but are also efficient and fast. The 2019 Toolkit was built to allow that standardize excellence in content but also to make assessments easier to create, customize and manage. The Toolkit is also built to work together to follow the typical process a third party risk practitioner would use to implement their program.
2019 Standardized Information Gathering (SIG) Questionnaire Tools
The 2019 SIG has undergone a major functionality and content reorganization. The SIG now functions as a questionnaire management tool that allows you to build, customize, analyze and store questionnaires.
Architecture – Questionnaires are now created from within the SIG Management Tool. Along with streamlined code, this makes the 2019 SIG size smaller, enabling questionnaires to be created more quickly. You can now create a SIG with questions all on one tab, or with a tab for each risk domain.
Content Library – There is no longer a “Full” SIG, but rather a database of member-vetted questions called the Content Library. The Content Library includes the SIG Core and the SIG Lite questions, but also houses industry-specific questions. You can even add custom questions to be treated and scored as any other included question.
Custom Scoping – Custom Scoping allows you to create the questionnaires you need without losing the benefits of standardizations by drawing from the Content Library. You now have three ways to edit a questionnaire – by control domain, by external requirement or by control category and subcategory.
Saved Questionnaires – A SIG questionnaire can now be saved as a template to be modified later, making it easy to create questionnaires for new vendors.
SCA Integration and Scoping – the 2019 SIG is now integrated with the Standardized Control Assessment (SCA) Procedure Tools for onsite and virtual assessments. You can now take a completed SIG and automatically create a SCA.
Content updates to the 2019 SIG Tools include;
Privacy and Compliance Updates – Updated with relevant and current U.S. and international regulatory and privacy requirements including an update of GDPR-related content.
Industry-Specific Content – Content Library additions including FDA content for Consumer Packaged Goods (CPG) and Life Sciences, Insurance industry-specific content and IoT (Internet of Things) content.
Mapping – The following nine mappings to Authority Documents are now included within the body of the SIG and can be used for creating questionnaires.
FFIEC APPENDIX J – Federal Financial Institutions Examination Council (FFIEC) Information Technology Examination Handbook – Appendix J: Strengthening the Resilience of Outsourced Technology Services, February 2015
FFIEC CAT Tool – FFIEC Cybersecurity Assessment Tool (CAT), May 2017
FFIEC MANAGEMENT HANDBOOK – FFIEC IT, IS & Outsourcing Examination Management Handbooks, November 2015
GDPR – EU General Data Protection Regulation (GDPR), April 2016 (Effective May 2018)
HIPAA – S. Department of Health and Human Services. Health Insurance Portability and Accountability Act (HIPAA) Simplification, March 2013
ISO 2700X – International Standards Organization (ISO) 27001/27002, 2013
NIST 800-53r4 – NIST 800-53r4 Security & Privacy Controls for Federal Information Systems and Organizations, January 2015
NIST CSF 1.1 – National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF), April 2018
PCI 3.2.1 – Payment Card Industry (PCI) PCI DSS V.3.2.1, February 2018
2019 Standardized Control Assessment (SCA) Procedure Tools
The SCA Tools are a standardized set of assessment procedures. When combined with the scoping features of the SIG, the 2019 SCA is a quick and efficient way to assess service providers during onsite or virtual assessments.
Enhancements to the 2019 SCA include;
Updated Guidance Documentation – The main SCA document includes new reference material that helps users complete assessments faster and with better understanding about the controls being assessed.
SCA Report Template – SCA reporting template is now in spreadsheet format, making it easier to document findings while onsite, copy and paste data and use on a mobile device.
Executive Summary Template – A new Executive Summary Template is included that will assist in creating a lightweight summary report of the SCA findings for management without all the detail of the full report.
SIG Integration and Automatic SCA Scoping – Using the SIG with its embedded SCA content, automatic customization is available to make SCA assessment procedures match just the SCA questions that were scoped and answered by the Assessee in a SIG.
SCA Assessment Standards for Distributable Reports – Due to the requirements within the SCA Standards for distributable reports, the outsourcer can be assured that the procedures in an SCA will be performed consistently, regardless of which certified organization performs it.
Content Updates
Privacy and Compliance Updates – Updated with relevant and current U.S. and international regulatory and privacy requirements including an update of GDPR-related content.
SIG Alignment – The SCA has been thoroughly reviewed and updated to align more closely with the SIG, using matching terminology and making it simpler to follow the “trust, but verify” model of third party risk management.
GDPR Privacy Tools Alignment – The GDPR Toolkit aligns completely with the SCA, ensuring SCA-based assessments address the most current privacy considerations.
2019 Vendor Risk Management Maturity Model (VRMMM) Benchmark Tools
The VRMMM, available since 2013, is the longest running third party risk maturity model, and has been vetted and refined by hundreds of the most experienced third party risk management professionals.
2019 saw significant updates to the VRMMM content, including;
Privacy and Compliance Updates – Updated with relevant and current U.S. and international regulatory and privacy requirements including an update of GDPR-related content.
Inclusion of recent guidance regarding Third Party Risk Management from:
The American Institute of Certified Public Accountants (AICPA) which sets guidelines for public auditing principles.
The Office of the Comptroller of Currency (OCC) which audits the safety and soundness of U.S. banks.
New York Department of Financial Services Part 500 of Title 23 of the Official Compilation of Codes, Rules and Regulations of the state of New York (NYDFS 23 NYCRR 500), which is a cybersecurity regulation mandated for any financial services company doing business in the U.S. state of New York.
Privacy requirements including the European Union General Data Protection Regulation (GDPR).
The VRMMM is important to third party risk, and we made it free to members and non-members. It can be download here.
2019 GDPR Privacy Tools
The GDPR Privacy Tools help meet the requirements imposed on how Controllers (i.e., outsourcers) must appoint and monitor Data Processors (i.e., third parties/vendors) as a part of GDPR.
Enhancements to the 2019 GDPR Privacy Tools include;
The GDPR Tool kit was originally released prior to the GDPR compliance deadline of May 25, 2018. The focus and narrative were on preparation for the upcoming deadline. Now that the deadline has passed, the leading practices incorporated in the tools have been updated based on the experiences of dozens of Shared Assessments member companies.
The template tools were enhanced to better allow tracking of issues over time.
Download this free tool.
Learn more about the Third Party Risk Management Toolkit
To learn more about the Toolkit updates, and to learn how the tools work together for a Third Party Risk Management Program, you can;
View a short demo of the 2019 SIG Questionnaire Tools changes.
View a short demo of how the Toolkit works together.
Attend a Live Demo