In December 2020, the cybersecurity industry faced its latest attack – SolarWinds. This hack reinforces the frailty of not only the software supply chain but the third-party vendor ecosystem. As more information is uncovered, it is becoming clear that this extensive ecosystem of vendors is the gateway for attackers to move laterally from network-to-network.
Tackling exponential risk in the software supply chain
The software supply chain presents an exponential risk as a compromised software channel can be used to push out malicious activity across a vast ecosystem. SolarWinds is unfortunately an example of this type of attack, which meant that when the adversaries got in, they could easily move across to other downstream victims.
Recent research undertaken by BlueVoyant with 1500 CIOs, CISOs and Chief Procurement Officers across six verticals and five countries showed the extent of unmanaged risk in the software supply chain and third-party vendor ecosystems.
The research helped to quantify the size of third-party vendor ecosystems and underlined that each vendor will have their own software supply chain, which compounds and multiplies the risk.
Cybersecurity breaches caused by third-party vendors
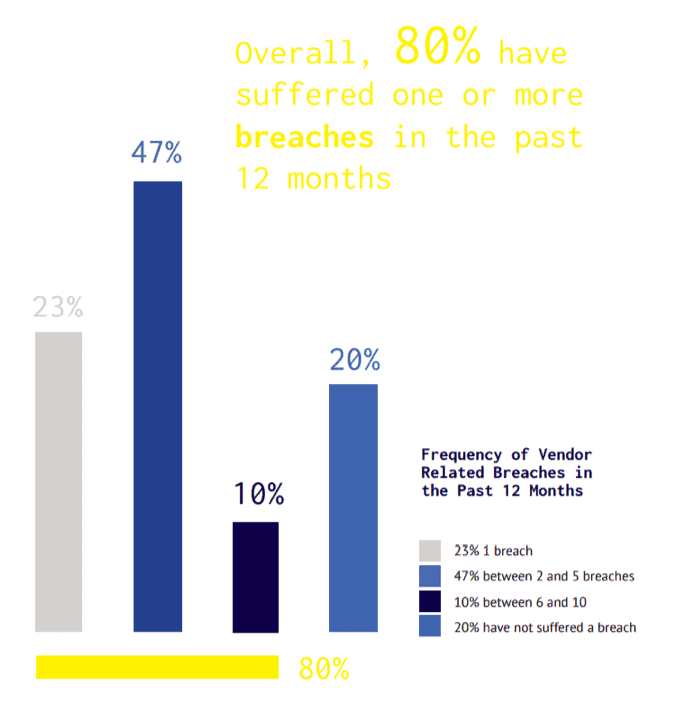
Overall, the research revealed that globally four in five firms surveyed (80%) had suffered a cybersecurity breach caused by a third-party vendor and the average respondent’s organisation had been breached in this way 2.7 times.
The size of the risk across different vertical sectors
Third-party cyber risk was evident in several key vertical sectors. Those that are particularly vulnerable operate within critical industries such as financial services, healthcare and pharmaceutical, and business services organisations (i.e., insurance, legal etc.) – all of whom have very large supplier ecosystems.

89% of business services organisations surveyed said they had suffered a breach because of weaknesses in their supply chain in the last 12 months, this figure was 86% among healthcare and pharmaceutical companies, 85% in financial services organisations. Other verticals were slightly lower with 80% in utilities companies, 79% in energy and 57% in manufacturing.
But it doesn’t stop there. If the risk of a data breach increases with third-parties, the likelihood is that this will introduce breach risk from fourth-and fifth-parties. Therefore, different verticals must consider who a vendor is outsourcing services to as well. Often a company outsources a service to a third-party and outsources specific functions to other vendors. Or, if they are using technology to deliver that service, they might contract it out to an external development house to undertake the software development. Here, the BlueVoyant research shows the number of vendors different vertical sectors are working with.
The SolarWinds hack is a wake-up call for the whole industry and across the board organisations must proactively bolster cybersecurity efforts with trusted vendors and security platforms within the supply chain.
Download The Full BlueVoyant research report
Download your copy of the full UK BlueVoyant research report – Global Insights: Supply Chain Cyber Risk – Managing Cyber Risk Across the Extended Vendor Ecosystem – today.
You’re Only As Strong As Your Weakest Link

There’s never been a more vital time to ensure the security of your organisation and the cyber supply chain you rely on. DVV Solutions are here to help with a range of managed services and solutions proven to improve your ability to assess, analyse and manage more cybersecurity and third-party risk domains.
For more information on enhancing your cybersecurity oversight:
Call Us: +44 (0) 161 476 8700
Contact Us: Complete our Contact Form, or
Learn more about What We Do
This article was originally published by BlueVoyant and is shared with their kind permission.
